Our oceans are acidifying — even if the nightly news hasn’t told you yet.
As humanity continues to fill the atmosphere with harmful gases, the planet is becoming less hospitable to life as we know it. The vast oceans absorb much of the carbon dioxide we have produced, from the industrial revolution through the rise of global capitalism. Earth’s self-sacrifice spared the atmosphere nearly 25 percent of humanity’s CO2 emissions, slowing the onslaught of many severe weather consequences.
Although the news media have increasingly covered the climate weirding of global warming — hurricane superstorms, fierce tornado clusters, overwhelming snowstorms, and record-setting global high temperatures — our ocean’s peril has largely stayed submerged below the biggest news stories.
The rising carbon dioxide in our oceans burns up and deforms the smallest, most abundant food at the bottom of the deep blue food chain. One vulnerable population is the tiny shelled swimmers known as the sea butterfly. In only a few short decades, the death and deformation of this fragile and translucent species could endanger predators all along the oceanic food web, scientists warn.
This “butterfly effect,” once unleashed, potentially threatens fisheries that feed over 1 billion people worldwide.
Since ancient times, humans fished the oceans for food. Now, we’re frying ocean life before we even catch it, starving future generations in the process. Largely left out of national news coverage, this dire report was brought to light by a handful of independent-minded journalists: Craig Welch from the Seattle Times, Julia Whitty of Mother Jones, and Eli Kintisch of ScienceNOW.
It is also the top story of Project Censored, an annual book and reporting project that features the year’s most underreported news stories, striving to unmask censorship, self-censorship, and propaganda in corporate-controlled media outlets. The book is set for release in late October.
“Information is the currency of democracy,” Ralph Nader, the prominent consumer advocate and many-time presidential candidate, wrote in his foreword to this year’s Project Censored 2015. But with most mass media owned by narrow corporate interests, “the general public remains uninformed.”
Whereas the mainstream media poke and peck at noteworthy events at single points in time, often devoid of historical context or analysis, Project Censored seeks to clarify understanding of real world issues and focus on what’s important. Context is key, and many of its “top censored” stories highlight deeply entrenched policy issues that require more explanation than a simple sound bite can provide.
Campus and faculty from over two dozen colleges and universities join in this ongoing effort, headquartered at Sonoma State University. Some 260 students and 49 faculty vet thousands of news stories on select criteria: importance, timeliness, quality of sources, and the level of corporate news coverage.
The top 25 finalists are sent to Project Censored’s panel of judges, who then rank the entries, with ocean acidification topping this year’s list.
“There are outlets, regular daily papers, who are independent and they’re out there,” Andy Lee Roth, associate director of Project Censored, told us. Too many news outlets are beholden to corporate interests, but Welch of the Seattle Times bucked the trend, Roth said, by writing some of the deepest coverage yet on ocean acidification.
“There are reporters doing the highest quality of work, as evidenced by being included in our list,” Roth said. “But the challenge is reaching as big an audience as [the story] should.”
Indeed, though Welch’s story was reported in the Seattle Times, a mid-sized daily newspaper, this warning is relevant to the entire world. To understand the impact of ocean acidification, Welch asks readers to “imagine every person on earth tossing a hunk of CO2 as heavy as a bowling ball into the sea. That’s what we do to the oceans every day.”
Computer modeler Isaac Kaplan, at the National Oceanic and Atmospheric Administration office in Seattle, told Welch that his early work predicts significant declines in sharks, skates and rays, some types of flounder and sole, and Pacific whiting, the most frequently caught commercial fish off the coast of Washington, Oregon, and California.
Acidification may also harm fisheries in the farthest corners of the earth: A study by the Arctic Monitoring and Assessment Programme outlines acidification’s threat to the arctic food chain.
“Decreases in seawater pH of about 0.02 per decade have been observed since the late 1960s in the Iceland and Barents Seas,” the study’s authors wrote in the executive summary. And destroying fisheries means wiping out the livelihoods of the native peoples of the Antarctic.
Acidification can even rewire the brains of fish, Welch’s story demonstrated. Studies found rising CO2 levels cause clown fish to gain athleticism, but have their sense of smell redirected. This transforms them into “dumb jocks,” scientists said, swimming faster and more vigorously straight into the mouths of their predators.
These Frankenstein fish were found to be five times more likely to die in the natural world. What a fitting metaphor for humanity, as our outsized consumption propels us towards an equally dangerous fate.
“It’s not as dramatic as say, an asteroid is hitting us from outer space,” Roth said of this slowly unfolding disaster, which is likely why such a looming threat to our food chain escapes much mainstream news coverage.
Journalism tends to be more “action focused,” Roth said, looking to define conflict in everything it sees. A recently top-featured story on CNN focused on President Barack Obama’s “awkward coffee cup salute” to a Marine, which ranks only slightly below around-the-clock coverage of the president’s ugly tan suit as a low point in mainstream media’s focus on the trivial.
As Nader noted, “‘important stories’ are often viewed as dull by reporters and therefore unworthy of coverage.” But mainstream media do cover some serious topics with weight, as it did in the wake of the police officer shooting of Michael Brown in Ferguson, Mo. So what’s the deciding factor?
As Roth tells it, corporate news focuses on “drama, and the most dramatic action is of course violence.”
But the changes caused by ocean acidification are gradual. Sea butterflies are among the most abundant creatures in our oceans, and are increasingly born with shells that look like cauliflower or sandpaper, making this and similar species more susceptible to infection and predators.
“Ocean acidification is changing the chemistry of the world’s water faster than ever before, and faster than the world’s leading scientists predicted,” Welch said, but it’s not getting the attention is deserves. “Combined nationwide spending on acidification research for eight federal agencies, including grants to university scientists by the National Science Foundation, totals about $30 million a year — less than the annual budget for the coastal Washington city of Hoquiam, population 10,000.”
Our oceans may slowly cook our food chain into new forms with potentially catastrophic consequences. Certainly 20 years from now, when communities around the world lose their main source of sustenance, the news will catch on. But will the problem make the front page tomorrow, while there’s still time to act?
Probably not, and that’s why we have Project Censored and its annual list:
2. TOP 10 US AID RECIPIENTS PRACTICE TORTURE
Sexual abuse, children kept in cages, extra-judicial murder. While these sound like horrors the United States would stand against, the reverse is true: This country is funding these practices.
The US is a signatory of the United Nations’ Convention against Torture and Other Cruel, Inhuman or Degrading Treatment or Punishment, but the top 10 international recipients of US foreign assistance in 2014 all practice torture, according to human rights groups, as reported by Daniel Wickham of online outlet Left Foot Forward.
Israel received over $3 billion in US aid for fiscal year 2013-14, according to a Congressional Research Service report. Israel was criticized by the country’s own Public Defender’s Office for torturing children suspected of minor crimes.
“During our visit, held during a fierce storm that hit the state, attorneys met detainees who described to them a shocking picture: in the middle of the night dozens of detainees were transferred to the external iron cages built outside the IPS transition facility in Ramla,” the PDO wrote, according to The Independent.
The next top recipients of US foreign aid were Afghanistan, Egypt, Pakistan, Nigeria, Jordan, Iraq, Kenya, Tanzania, and Uganda. All countries were accused of torture by human rights groups such as Amnesty International and Human Rights Watch.
Kenyan police in Nairobi tortured, raped, or otherwise abused more than 1,000 refugees from 2012 to 2013, Human Rights Watch found. The Kenyan government received $564 million from the United States in 2013-14.
When the US funds a highway or other project that it’s proud of, it plants a huge sign proclaiming “your tax dollars at work.” When the US funds torturers, the corporate media bury the story, or worse, don’t report it at all.
3. TRANS-PACIFIC PARTNERSHIP, A SECRET DEAL TO HELP CORPORATIONS
The Trans-Pacific Partnership is like the Stop Online Piracy Act on steroids, yet few have heard of it, let alone enough people to start an Internet campaign to topple it. Despite details revealed by Wikileaks, the nascent agreement has been largely ignored by the corporate media.
Even the world’s elite are out of the loop: Only three officials in each of the 12 signatory countries have access to this developing trade agreement that potentially impacts over 800 million people.
The agreement touches on intellectual property rights and the regulation of private enterprise between nations, and is open to negotiation and viewing by 600 “corporate advisors” from big oil, pharmaceutical, to entertainment companies.
Meanwhile, more than 150 House Democrats signed a letter urging President Obama to halt his efforts to fast-track negotiations, and to allow Congress the ability to weigh in now on an agreement only the White House has seen.
Many criticized the secrecy surrounding the TPP, arguing the real world consequences may be grave. Doctors Without Borders wrote, “If harmful provisions in the US proposals for the Trans-Pacific Partnership (TPP) agreement are not removed before it is finalized, this trade deal will have a real cost in human lives.”
4. CORPORATE INTERNET PROVIDERS THREATEN NET NEUTRALITY
This entry demonstrates the nuance in Project Censored’s media critique. Verizon v. FCC may weaken Internet regulation, which Electronic Frontier Foundation and other digital freedom advocates allege would create a two-tiered Internet system. Under the FCC’s proposed new rules, corporate behemoths such as Comcast or Verizon could charge entities to use faster bandwidth, which advocates say would create financial barriers to free speech and encourage censorship.
Project Censored alleges corporate outlets such as The New York Times and Forbes “tend to highlight the business aspects of the case, skimming over vital particulars affecting the public and the Internet’s future.”
Yet this is a case where corporate media were circumvented by power of the viral web. John Oliver, comedian and host of Last Week Tonight on HBO, recently gave a stirring 13-minute treatise on the importance of stopping the FCC’s new rules, resulting in a flood of comments to the FCC defending a more open Internet. The particulars of net neutrality have since been thoroughly reported in the corporate media.
But, as Project Censored notes, mass media coverage only came after the FCC’s rule change was proposed, giving activists little time to right any wrongs. It’s a subtle but important distinction.
5. BANKERS REMAIN ON WALL STREET DESPITE MAJOR CRIMES
Bankers responsible for rigging municipal bonds and bilking billions of dollars from American cities have largely escaped criminal charges. Every day in the US, low-level drug dealers get more prison time than these scheming bankers who, while working for GE Capital, allegedly skimmed money from public schools, hospitals, libraries, and nursing homes, according to Rolling Stone.
Dominick Carollo, Steven Goldberg, and Peter Grimm were dubbed a part of the “modern American mafia,” by the magazine’s Matt Taibbi, one of the few journalists to consistently cover their trial. Meanwhile, disturbingly uninformed cable media “journalists” defended the bankers, saying they shouldn’t be prosecuted for “failure,” as if cheating vulnerable Americans were a bad business deal.
“Had the US authorities decided to press criminal charges,” Assistant US Attorney General Lanny Breuer told Taibbi. “HSBC (a British bank) would almost certainly have lost its banking license in the US, the future of the institution would have been under threat, and the entire banking system would have been destabilized.”
Over the course of decades, the nation’s bankers transformed into the modern mafioso. Unfortunately, our modern media changed as well, and are no longer equipped to tackle systemic, complex stories.
6. THE “DEEP STATE” OF PLUTOCRATIC CONTROL
What’s frightening about the puppeteers who pull the strings of our national government is not how hidden they are, but how hidden they are not.
From defense contractors to multinational corporations, a wealthy elite using an estimated $32 trillion in tax-exempt offshore havens are the masters of our publicly elected officials. In an essay written for Moyer and Company by Mike Lofgren, a congressional staffer of 28 years focused on national security, this cabal of wealthy interests comprise our nation’s “Deep State.”
As Lofgren writes for Moyers, “The Deep State is the big story of our time. It is the red thread that runs through the war on terrorism, the financialization and deindustrialization of the American economy, the rise of a plutocratic social structure and political dysfunction.”
This is a story that truly challenges the mass media, which do report on the power of wealth, in bits and pieces. But although the cabal’s disparate threads are occasionally pulled, the spider’s web of corruption largely escapes corporate media’s larger narrative.
The myopic view censors the full story as surely as outright silence would. The problem deepens every year.
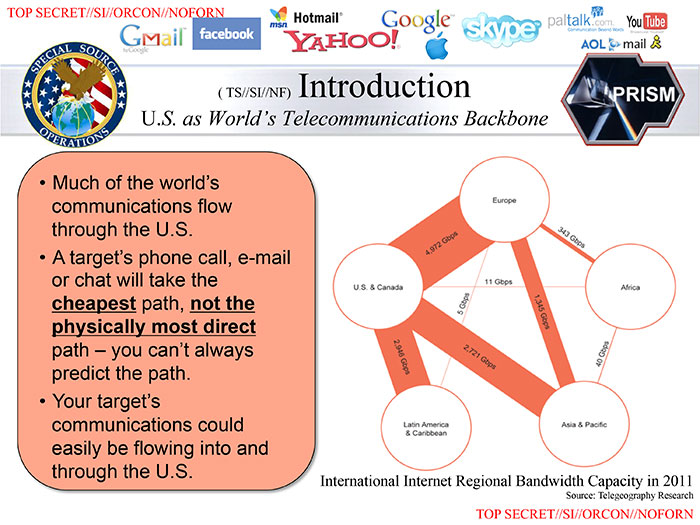
“There are now 854,000 contract personnel with top-secret clearances — a number greater than that of top-secret-cleared civilian employees of the government,” Lofgren wrote, of a group that together would “occupy the floor space of almost three Pentagons — about 17 million square feet.”
7. FBI DISMISSES PLOT AGAINST OCCUPY AS NSA CRACKS DOWN ON DISSENT
Nationally, law enforcement worked in the background to monitor and suppress the Occupy Wall Street movement, a story the mainstream press has shown little interest in covering.
A document obtained in FOIA request by David Lindorff of Who, What WHY from the FBI office in Houston,, Texas revealed an alleged assassination plot targeting a Occupy group, which the FBI allegedly did not warn the movement about.
From the redacted document: “An identified [DELETED] as of October planned to engage in sniper attacks against protestors (sic) in Houston, Texas if deemed necessary. An identified [DELETED] had received intelligence that indicated the protesters in New York and Seattle planned similar protests in Houston, Dallas, San Antonio and Austin, Texas. [DELETED] planned to gather intelligence against the leaders of the protest groups and obtain photographs, then formulate a plan to kill the leadership via suppressed sniper rifles.”
Lindorff confirmed the document’s veracity with the FBI. When contacted by Lindorff, Houston Police were uninterested, and seemingly (according to Lindorff), uninformed.
In Arizona, law enforcement exchanged information of possible Occupy efforts with JP Morgan Chase CEO Jamie Dimon, according to a report by the Center for Media and Democracy titled Dissent on Terror. The CEO meant to evade possible protests, and local law enforcement was happy to help.
Law enforcement’s all-seeing eyes broadened through the national rise of “fusion centers” over the past decade, hubs through which state agencies exchange tracking data on groups exercising free speech. And as we share, “like,” and “check-in” online with ever-more frequency, that data becomes more robust by the day.
8. IGNORING EXTREME WEATHER CONNECTION TO GLOBAL WARMING
In what can only be responded to with a resounding “duh,” news analyses have found mainstream media frequently report on severe weather changes without referring to global warming as the context or cause, even as a question.
As Project Censored notes, a study by Fairness and Accuracy in Reporting found extreme weather events in 2013 spurred 450 broadcast news segments, only 16 of which even mentioned climate change. National news outlets have fallen on the job as well, as The New York Times recently shuttered its environmental desk and its Green blog, reducing the number of reporters exclusively chasing down climate change stories.
Unlike many journalists, ordinary people often recognize the threat of our warming planet. Just as this story on Project Censored went to press, over 400,000 protested in the People’s Climate March in New York City alone, while simultaneous protests erupted across the globe, calling for government, corporate, and media leaders to address the problem.
“There is a huge mismatch between the magnitude of the challenge and the response we heard here today,” Graca Machel, the widow of former South African President Nelson Mandela, told the United Nations conference on climate change. “The scale is much more than we have achieved.”
9. US MEDIA HYPOCRISY IN COVERING UKRAINE CRISIS
The US battle with Russia over Ukraine’s independence is actually an energy pipeline squabble, a narrative lost by mainstream media coverage, Project Censored alleges.
Russian President Vladimir Putin has drawn fire from the media as a tyrant, without complex analyses of his country’s socio-economic interests, according to Project Censored. As the media often do, they have turned the conflict into a cult of personality, talking up Putin’s shirtless horseback riding and his hard-line style with deftness missing from their political analysis.
As The Guardian UK’s Nafeez Ahmed reported, a recent US State Department-sponsored report noted “Ukraine’s strategic location between the main energy producers (Russia and the Caspian Sea area) and consumers in the Eurasian region, its large transit network, and its available underground gas storage capacities,” highlighting its economic importance to the US and its allies.
10. WORLD HEALTH ORGANIZATION SUPPRESSES REPORT ON IRAQ IMPACTS
The United States’ legacy in Iraq possibly goes beyond death to a living nightmare of cancer and birth defects, due to the military’s use of depleted uranium weapons, a World Health Organization study found. Iraq is poisoned. Much of the report’s contents were leaked to the BBC during its creation. But the release of the report, completed in 2012 by WHO, has stalled. Critics allege the US is deliberately blocking its release, masking a damning Middle East legacy rivaling the horrors of Agent Orange in Vietnam. But Iraq will never forget the US intervention, as mothers cradle babies bearing scars obtained in the womb, the continuing gifts of our invasion.